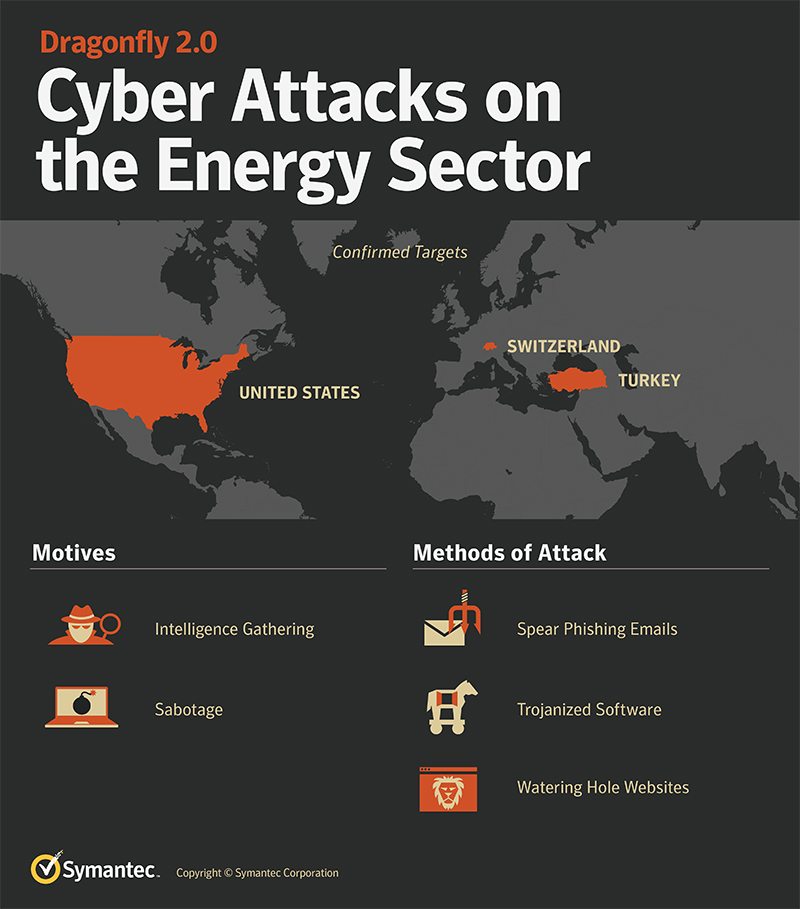
The United States is now facing serious security threat as a latest hacking attack gave cyber criminals access to energy companies which control major parts of the power grid that supplies electricity to millions of its citizens.
Aside from the United States, European energy companies were also targeted by this latest hacking attack. The incident was uncovered by Symantec, a U.S.-based cybersecurity firm. In a post published by Symantec on its website, the security company said:
“The energy sector in Europe and North America is being targeted by a new wave of cyber attacks that could provide attackers with the means to severely disrupt affected operations.”
Further investigation suggests that the hacking incident was executed by a group known as Dragonfly. According to Symantec, the group has been in operation since 2011 but went dark in 2014 when the company and other online security researchers exposed them.
#Dragonfly staged latest hacking attack which targets #US power grid networks!Click To TweetLatest Hacking Attack by Dragonfly is Troubling
For the past two years, cyber attackers have shown keen interest on the energy sector. It should be noted that in July, an unknown group of hackers executed a campaign to infiltrate several nuclear power plants and energy companies in the U.S.
While the identity of the said hackers was not exposed, people familiar with the case claimed that the techniques utilized by the group resembled those of the Russian hacking group known as Energetic Bear.
Another notable energy hacking incident happened in Ukraine in 2015 and 2016 were cyber attackers caused massive power outages that affected hundreds of thousands of people. Other European countries also confirmed several attempts at hacking their electricity grids.
With the case of Dragonfly, it appears that the group is interested in two things: learning how energy facilities work and gaining access to the operational systems themselves. The cyber criminals’ latest hacking attack has potentially given them the ability to sabotage or gain control of power grid systems.
“There’s a difference between being a step away from conducting sabotage and actually being in a position to conduct sabotage … being able to flip the switch on power generation,” says Eric Chien, a Symantec security analyst in a statement to Wired.
“We’re now talking about on-the-ground technical evidence this could happen in the US, and there’s nothing left standing in the way except the motivation of some actor out in the world,” he went on to say.
The Dragonfly 2.0 Campaign
According to Symantec, the evidence they obtained shows that Dragonfly 2.0 campaign has been ongoing since 2015. The security firm also pointed out a significant increase in the campaign’s activity this 2017.
The escalation is deemed by experts as troubling because operational networks can often wield significant influence over the stability of the electric grid they’re responsible for.
Apparently, cyber criminals who have access to an energy company’s power grid operation could pose as de facto operators of the company’s energy assets. Such control can give the attackers power over the breakers inside the companies’ infrastructure, and the ability to hijack energy health monitor systems.
If that is not alarming enough, the latest hacking attack provides an opportunity for the hackers to create failures in multiple grid-connected operational networks that could lead to a major blackout, pretty much like the Northeast Blackout of 2003.
How were the power grid networks got infiltrated by hackers? Symantec explained:
“As it did in its prior campaign between 2011 and 2014, Dragonfly 2.0 uses a variety of infection vectors in an effort to gain access to a victim’s network, including malicious emails, watering hole attacks, and Trojanized software.
The group conducted further targeted malicious email campaigns during 2016 and into 2017. The emails contained very specific content related to the energy sector, as well as some related to general business concerns. Once opened, the attached malicious document would attempt to leak victims’ network credentials to a server outside of the targeted organization.”
Aside from malicious emails, the attackers also used “watering hole attacks to harvest network credentials, by compromising websites that were likely to be visited by those involved in the energy sector.”
After stealing credentials, the attackers executed a series of follow-up attacks against their target organizations. In one scenario, Backdoor.Goodor, which provides attackers remote access to a victim’s machine, was said to have been installed on a victim’s machine via PowerShell, 11 days after visiting a compromised server.
According to a report from The Guardian, the group appears to be more interested in information-gathering. However, Symantec warns that a quiet beginning is often a prelude to deliberate attempts at sabotage.
“Sabotage attacks are typically preceded by an intelligence-gathering phase where attackers collect information about target networks and systems and acquire credentials that will be used in later campaigns.”
Right now, security experts are having a hard time identifying where the latest hacking attack and the group behind it originated. Some of the codes found in the Dragonfly campaign were said to be in Russian and French.
“Conflicting evidence and what appear to be attempts at misattribution make it difficult to definitively state where this attack group is based or who is behind it,” Symantec said.



















Comments (0)
Most Recent