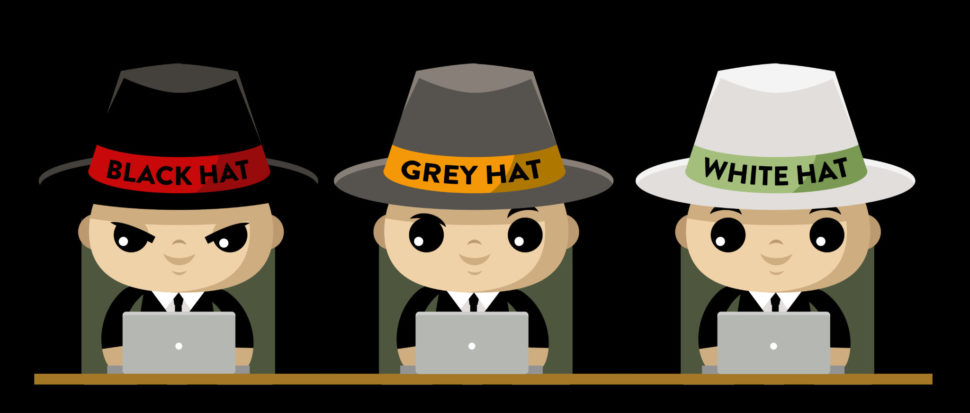
You may be familiar with the terms “white hat”, “black hat”, and “grey hat”, but what do they really mean?
As we move further towards an IoT future, interconnectivity is both a gift and a curse. If everything is connected, everything is vulnerable. But this also means that those vulnerabilities can be exploited for good causes.
Is there such a thing as “ethical hacking”?
Ethical #Hacking: How to Hack for GoodClick To TweetFirst, Let’s Define How White, Black, and Grey Refer to Hacking
The first thing to know about potential “ethical hacking” is that it doesn’t necessarily require ethical means by which you hack. If you are hacking a private security database, but not leaking the data to show how easily people’s privacy can be violated, you might be a grey hat hacker.
But let’s break that down: you can use any hacking means for any hacking goals. Think of it like a bingo board with white, black, and grey squares. Applying the terms “white”, “black”, and “grey” works similarly to how you might expect it to based on storytelling conventions.
- White relates to a security specialist or hacker assessing network security; traditionally “above board” hackers who have permission from an organization or company
- Grey relates to hackers or security specialists who may employ tactics from both white and black camps but could also relate to individuals whose goals don’t fall into “white” or “black” depending on perspective
- Black relates to hackers treated as malicious; security breachers who exploit vulnerabilities in security for personal gain
Tangible examples of these archetypes in action include Elliot from the tv series Mr. Robot. He serves in any of the three categories depending on which part of the show it is.
Another classic example is the teenagers in the 1990s film Hackers. A private sector hacker tries to frame them for black hat hacking, so they incorporate grey hat strategies to save themselves and out the actual bad guy.
But what are some real-world examples of each type of hacker and is there such a thing as ethical hacking?
The Epic Rise and Degradation of WikiLeaks as a Vigilante Hacking Group
One of the first mainstream hacking groups that started leaking information on a large scale was WikiLeaks. It started out as a source of information, specifically aimed at the United States in many ways. The mission was to avoid authoritarian, information-limited societies and to expose “secrets” for the common good.
You could loosely argue that WikiLeaks originated as a white hat hacking group before “white hat” came to solely mean security professionals. The group pursued its mission, usually releasing information that did not harm individuals.
As the group adapted over the years, however, its objective became muddled with allegations against its editor-in-chief Julian Assange. Coupled with the standing Russia conspiracy surrounding the most recent 2016 presidential election in the U.S., WikiLeaks has changed from a white hat organization into a grey hat organization.
More realistically, the organization shifted from a lighter grey to a darker color over the last few years. In trying to disperse information in more effective or provocative manners, some question if people’s information is threatened by this group that initially wanted to help the common people.
The reason for this: a shift in perspective and strategies along with allies. One other main hacking group makes headlines often. But many initially thought they were far more dangerous than WikiLeaks.
Where do Groups Like Anonymous Fall?
There are definite ethical lines when it comes to delineating grey hat hackers from black hat hackers. Ethical hacking requires adhering to a similar set of ethics or morals that the majority of society do. Blackmailing major companies for financial gain falls into the black hat category.
But many hacking groups don’t fear notoriety nor do they feel the need to live in obscurity. Vice chatted with some hackers from Basehack who were very open about making “hundreds of thousands of dollars a year”. But, they never hacked charities; mostly, they exploited “stupid” businesses (businesses with obvious security vulnerabilities).
Anonymous, loosely formed on a 4chan image board in 2003, went to bat for WikiLeaks once upon a time. Their hacking records ranges from Sony to Mastercard to the country Iran and more.
Anonymous has openly “declared war” on individuals it feels pose threats such as Donald Trump, Hillary Clinton, and Aaron Barr, someone who tried to finger Anonymous leadership. The group is very secular, claiming it has no official leadership.
These hackers also put members in two separate camps: white and black. Some, such as “Gary in the White Hat” who spoke with Huffington Post, operate in mostly legal, moral ways. Most of the members maintain a “black” or “white” status.
The group eschews the term “grey hat” in that it implies co-mingling. Again, Anonymous maintains a stance of loose associations, so it follows that the white vs. black hat hackers wouldn’t necessarily be in contact. Despite this, Anonymous could also be viewed as a “grey hat” group.
Ethical hacking is not outside their realm of actions…but it also isn’t their only focus either.

How Corporations and the Government Use Hackers to Better Their Security
White hat hackers are totally above board. In the very first episode of Mr. Robot, Elliot is recruited by the company he works for (Allsafe) to stop a DDoS attack on a client.
Due to his skillset, he becomes entrenched in helping find the perpetrator when he backtraces how the system was hacked. Of course, without spoiling how the show goes, it becomes much more complex than that.
But you see how having someone with knowledge of hacking strategies such as phishing, malware, DDoS, keystroke, or brute force hacking can be beneficial for a major company. It’s a turn toward the future many companies such as Equifax ought to consider moving forward. If you know how the enemy is going to fight you, you can better prepare your defenses.
In that same vein, online and real-world universities like Udemy and Berkeley now offer ethical hacking courses. You can become a Certified Ethical Hacker in no time at all. While black hat hacking can be profitable, white hat hacking can be, too.
The most practical, benevolent use of a hacker’s skills are employing them for bug bounties. These employ “hackers” to infiltrate a given company’s or government agency’s network or software suite to find bugs. This way, the developer is aware of flaws before bad actors find them out in the “wild”.
Ultimately, what the companies do with the result of their white hat hackers is what determines whether or not it is “ethical hacking”. That’s the troubling aspect of white hat work. You are a contractor selling your skills, but you have no real sway over how your work gets used when it is done.


















Contact Leonardo today for any infidelity Issues.
He helped me to get into my husband’s phone remotely and he helped me to gain justice to my husband’s infidelity activities. He is professional and nice hacker to work with …Contact him on his email for hire or to know more about his services
Leonardomitnickhacking@gmail. com
Or whatsapp him via +1 305 440 5462
Are you looking to get the best hacker to hire with perfect assurance that your job will be done perfect without any traces. as the properties of a perfect hacker is anonymous ftp, which they guarantee you can contact kelvinethicalhacker @ gmail.com, for any hacking services, if you need a reliable hacker who will never delay your work and give you result within 6 hours you all should text him whatsApp + 1 (341)465-4599, he can help you hack any devices phone without the person knowing is phone has been hacked.,,,,..,,
There are many ways to link or clone your partners’ phone to yours, with the help of experts { stealthyhacks@gmailcom }, such task can be accomplished, it takes great expertise of theirs to get such task in to fruition. I am a testament of their service hence the reason for recommending their services.
I have used the expertise of StealthyHacks@Gmail. Com and he was absolutely tremendous at what he does.
The best expert to reach out to is RecoveryBureauC @Gmail, c0m to remotely monitor a cheating partner’s phone and upgrade bad grades. You can reach him on WhatsApp: +44 7586 868096
RecoveryBureauC (at)g m ail,c0m is truly the best tech expert out here who can remotely trace and track your suspected cheating spouse phone to gain vivid and clear proof of their cheating ways. He’s the real deal!!!
I was looking for the best and fast app to trace, track and monitor my spouse activities on her phone after I discovered she’s been acting strange lately and taking late night calls. Then I came on the internet to hire a genuine techie to remotely monitor her phone I got introduced to RECOVERYBUREAUC @ GMAIL, C0M and I thank my stars he was indeed competent and legit. He got me access to my spouse phone like I got her phone in my palm and it was all done discretely. Then I figured out she has been cheating all along the relationship. He is the only genuine and the best tech guru to hire for all tech services from full mobile phone cloning to retrieval of lost/stolen digital assets
contact details: RECOVERYBUREAUC(at)GMAIL, C0M.. This is a total pro and the best
Everyday I wake, I am very glad I hired this great hacker Viktor. This man helped me hack an iPhone within 6 hours. I could read all messages on the phone, emails, access to photos/ videos and an option to listen to phone calls. I was never the kind of guy to believe in hackers but I guess I was wrong all along. IF YOU NEED A HACKER, CONTACT VIKTOR VIA EMAIL: viktorhackworld @ gmail. com
He offers so many other services, it’s a long list.
Last week I had a suspicion on my spouse seeing someone else but I couldn’t get clear and vivid proof to catch her redhanded in her sneaky ways so I decided to come on the internet to find a genuine and competent mobile phone monitoring expert who can grant me remote access to her phone then I found RECOVERYBUREAUC (at) G M AIL, C0M who came to my rescue and gave me access to see all of her hidden texts, call history, social media contents etc then I figured out she’s been cheating all along the relationship. The best techie that offers outstanding tech services is
RECOVERYBUREAUC @ GMAIL, C0M.. This is the real deal, you can reach him on WhatsApp: +44 7586 868096
I’ ve got unlimited access to my husbands iPhone and PC and also have his activities in check thanks to this dude who is a Russian Hacker by his name Yuri I got introduced to from the UK who helped my friend boost her credit score. His assistance really meant a lot to me. I got access to my
husband’s cell phone, WhatsApp calls, without his knowledge with just his cell phone number this badass did everything remotely, I don’t know.if it’s right to post his contact but I promised him referrals, alot of fake ass out here, also someone might need his help so welp. I’m grateful to Yuri.
Email is spyhackpro9 @gmail com
Good work always speak for itself, you should contact him!
The perfect way to know if your other significant is seeing someone else in your marriage or relationship is to lookup RecoveryBureauC (at) g m a i L. I got help via this means and would want others going through this dark path get the appropriate help. Having a suspicion on your spouse cheating is a great heart ache especially when you don’t have proofs to back up your claims.. Info: RECOVERYBUREAUC @ GMAIL, C0M
Life can be ridiculous at times, and it gets even worse when you have a cheating spouse. Thanks to a friend who introduced me to a sophisticated hacker who assisted me in obtaining all secret files that my husband had been hiding for several years of our marriage. He assisted in hacking and gaining access to my cheating husband’s icloud, social media networks, call log and spy call recording, monitoring SMS text messages remotely, cell phone GPS location tracking, spying on WhatsApp Messages, gmail, and kik, and I discovered he had done me dirty. The hacker is discrete and proactive in his work; you can reach him at hackrontech @gmail com. You won’t be sorry if you give him a shot today
HOW I FOUND OUT MY WIFE WAS CHEATING THROUGH GEARHEAD ENGINEERS
I was one of many men who never thought a day would come when my wife would cheat on me. I found out when my friend and I jokingly got a hacker to spy on our wives’ phones. There were no signs at all of her infidelity so I was 100% sure that I wouldn’t get anything suspicious in her phone. On the other hand, my friend had doubts based on his wife’s recent behaviour. We got a cyber company called GearHead Engineers to do the job and they immediately sent us instructions which later gave us access to the women’s phones. The shock I felt when I checked her WhatsApp and messages is hard to describe. My wife is the sweetest and most caring woman on earth and there was no way I would ever imagine her hurting me in any way. But surprisingly, she had been sleeping with our son’s coach for what seemed like months. I ambushed her and her defence was that she got lonely because I no longer give her attention and affection but the truth is that I have been occupied with work since I am the breadwinner. I somehow understand her but at the same time I feel no emotion. I love my family and I don’t want us to go through the agony of divorce. What should I do?
RECOVER YOUR LOST/STOLEN BITCOIN WITH THE HELP OF CRYPTO RECOVERY WIZARD
When it comes to retrieving stolen bitcoin, CRYPTO RECOVERY WIZARD is unique due to its skill, dedication, and experience. Knowing the ins and outs of the cryptocurrency world, they work closely with law enforcement and utilize cutting edge methods to locate and track down stolen bitcoin. Their exceptional reputation in the bitcoin recovery services industry stems from their individualized approach and unwavering dedication to client satisfaction. My bitcoin was stolen, and although I reached out to several hackers who said they could help me get it back, all they did was take additional money from me in the process. Upon reaching out to CRYPTO RECOVERY WIZARD for support, all hope was reestablished. I was first skeptical, but CRYPTO RECOVERY WIZARD eventually managed to retrieve my bitcoin. Thank you very much. contact CRYPTO RECOVERY WIZARD for help to get your ust/stolen funds back and be happy.
Email: hackrontech@ gmail.com
EASIEST WAY TO HIRE A PHONE HACKER CALLED GEARHEAD ENGINEERS
I have always wanted the best for my only son because I want him to experience the best the world can offer. This includes him ending up with a good woman. One thing about marriage, you know, is that the person you choose to spend the rest of your life with determines your happiness for the the rest of your life. I have been skeptical of every woman my son has brought around and I make sure I get to investigate before my son gets heartbroken. 2 years ago, a friend of mine shared on how she uses hackers to spy on her husband and so I got the idea to do a little bit of research on my potential daughters in-law. I casually asked for the hackers’ information and since then, I spy on every girl he introduces me to. The process is pretty simple, you send an email to gearhead @ engineer . com of the phone number of the person you want to spy on and after a few hours, they will send you the exact info you need. I have saved my son from 2 women who were eventually going to ruin his life and even though he will never find out what I have been doing, I am content that he has dodged deadly bullets.
Are you looking to get the best hacker to hire with perfect assurance that your job will be done perfect without any traces. as the properties of a perfect hacker is anonymous ftp, which they guarantee you can contact kelvinethicalhacker @ gmail.com, for any hacking services, if you need a reliable hacker who will never delay your work and give you result within 6 hours you all should text him whatsApp + 1 (341)465-4599, he can help you hack any devices phone without the person knowing is phone has been hacked…
Are you looking to get the best hacker to hire with perfect assurance that your job will be done perfect without any traces. as the properties of a perfect hacker is anonymous ftp, which they guarantee you can contact kelvinethicalhacker @ gmail.com, for any hacking services, if you need a reliable hacker who will never delay your work and give you result within 6 hours you all should text him whatsApp + 1 (341)465-4599, he can help you hack any devices phone without the person knowing is phone has been hacked,.,,.
A vary big thanks to hackrontech @gmail com for the great the work you done for me, i got the email address on the net web when i needed to hack ny husband cell phone he helped me within few hourse with whatsApp hacking and GPS location tracking direct from my person phone i know how my husband walks, thanks for the helped you do for me for every greatfull for your helped, you can contact him through gmail via hackrontech @gmail com if you are in needed of hacking services, contact him for your own helped.
I have spent so much time looking for a way to remove the negatives items impacting on my credit report. A friend of mine introduced me to this credit expert, I doubted the process at first because I was ripped off by some other person I met online So i had no hope than to take the risk, so i contact him to help me fix my credit score and clear off my criminal record. He increased my credit score from 480 to 800 . Contact him for your credit repair on his regular email GOLDCREDITFIX At Gmail Dot Com
Relationship are sometimes complicated. They are built on one key parameter which is trust but sometimes people tend to take advantage of the ones they were suppose to love and nothing else. There is no room for cheating in a relationship that’s being said YES. It’s quite subjective. Nevertheless, hurting your significant other feelings can be a heartbreaking thing for any person.
Spying on someone without the knowledge is unethical unless you are sure the person is up to something which might hurt you physically or emotionally. In this modern age where everything is either smart or going to be, the means of communication is always very smart which means that you can keep a track of someone’s conversation.
If you are in a relationship and you want to keep track of your Cheating spouse messages, there are lots of ways to do that with the help of the tech genius.
Email; StealthyHacks@G mail. Com
Beyond reasonable doubt, Kev ; DcipherBlaze at G mail dot Com, is the most reliable and diligent tech guy I’ve ever met online, he does this app that gives people access to another phone that is entirely out of their jurisdiction effortlessly. I am vouching for his expertise, send him a mail if you need such help.
A great hacker is really worthy of good recommendation , Hackerone975
really help to get all the evidence i needed against my husband and
and i was able to confront him with this details from this great hacker
to get an amazing service done with the help of Hackerone975 contact him on: Hackerone975 @ gmail com
Are you worried your husband might be cheating on you? Do you want to spy on their chats, calls and text messages? Do you want to get notifications of the places they visit? they can do all these and more. He clone mobile phones thereby delivering intercepted messages in real time. Catch them red handed. He can get you all the evidence you need. Write to her at hack4wise @gmail com and thank me later
My ex fiance was cheating on me but I had no proof and I felt crazy and paranoid at that time, I even felt I was losing my mind. I needed closure badly and I hired hack4wise @gmail com although it’s unethical and it’s something i had to do. just tell him i sent you… Though I am not proud of what I did but I had no choice, I was almost driven to the brink of suicide , he can
I just caught my best friend trying to sleep with my husband with the help of spyexpert0 @ gmail. com She copied my husband number from my phone, still asking my self how she was Able to unlock my phone. when she finally got in contact with my husband she told him how she took the number and to tell you how stupid my husband is he also decided to cheat on me with her. Am just thankful to you spyexpert0 @ gmail. com for your services when it comes to phone hacking this is the 2nd time using your services and it still came out💯 successful.
Last week I had a suspicion on my spouse seeing someone else but I couldn’t get clear and vivid proof to catch her redhanded in her sneaky ways so I decided to come on the internet to find a genuine and competent mobile phone monitoring expert who can grant me remote access to her phone then I found RECOVERYBUREAUC (at) G M AIL, C0M who came to my rescue and gave me access to see all of her hidden texts, call history, social media contents etc then I figured out she’s been cheating all along the relationship. The best techie that offers outstanding tech services is
RECOVERYBUREAUC @ GMAIL, C0M
I was looking for the best and fast app to trace, track and monitor my spouse activities on her phone after I discovered she’s been acting strange lately and taking late night calls. Then I came on the internet to hire a genuine techie to remotely monitor her phone I got introduced to RECOVERYBUREAUC @ GMAIL, C0M and I thank my stars he was indeed competent and legit. He got me access to my spouse phone like I got her phone in my palm and it was all done discretely. Then I figured out she has been cheating all along the relationship. He is the only genuine and the best tech guru to hire for all tech services from full mobile phone cloning to retrieval of lost/stolen digital assets
contact details: RECOVERYBUREAUC(at)GMAIL, C0M
WhatsApp: +44 7586 868096
I was able to secretly monitor my cheating wife’s activities when I looked up the best phone monitoring and bad repair expert at RecoveryBureauC (at)g Mail, c0m. He’s the best!!
Catch your cheating partner redhanded in their sneaky ways when you hire RECOVERYBUREAUC @ GMAIL, c0m. This was the expert that saved me from my cheating wife couple of weeks ago when I had a suspicion on her but couldn’t figure out exactly her ways. I was fortunate to hire this genuine tech pro to remotely access my wife’s cellphone and gave me access to her phone files ranging from iMessage, text messages, call history, Snapchat, gallery, videos etc. All these contents were both hidden, current and deleted files. This was how I got to know about her love affair with a colleague at her work place. I was shocked about all the details I retrieved but I’m glad that I’m freed from the shackles of a cheater. I’m currently in our divorce proceedings and this files are really helping me out in the court cases. Many thanks to RECOVERYBUREAUC @ GMAIL, c0m for rendering this intellectual phone monitoring service.
Email: RECOVERYBUREAUC @ GMAIL, C0M
WhatsApp: plus four four seven five eight six eight six eight zero nine six..
I was frustrated and depressed when i noticed my spouse was cheating on me and there was nothing i could do about it, one day i saw an ad by this hacker and decided to contact him we got to talking and he has been helping me ever since; right now i am in the final stages of my divorce getting what i deserve all thanks to them . you should contact him if you have any legit hacking related issues wisetechacker @gmail com
Thank your stars for having the privilege to read this cause a lot of people out there are suffering and got no solution to their problems but I’m sure you gonna get yours through RecoveryBureauC @ gmail c0m by reading through my life drama. It’s so sad to share my story on here but I just want to let you all know especially those going through hard times in their relationships you are not left alone you just need to get the right hands to help you. After several months of having an affair with a bully, which was his newly embraced attitude initially when we met he was the best thing that ever happened to me cause he never wanted me sad he cares a lot and get the right things done. A few months afterwards he started putting up strange attitudes like keeping late nights, getting drunk, chatting with some thrash girls downtown and lot more. Anytime I complain I get a slap on the wrist, I couldn’t continue with this life has it hurts me badly each and everyday of my life. All I ever wanted was a good home, peace of mind and enjoy a good life but I wasn’t getting that this feeling got me sick until a certain day I got the courage and I sought for help. I came on the internet despite not being a safe place, I got the most ever needed help of my life from this super smart genius IT expert/ private investigator ( RECOVERYBUREAUC(@) GMAIL C0M ). Thank God I met Greg and he was the real deal, I saw great recommendations about him on how he helped others in their relationship, I contacted him within few minutes I got a response with some instructions and he requested for little info off his phone which I did gave him. In a short space of time, I got an email he’s got access to his phone without physical touch he sent all of his conversations with the girls ranging from text messages, call logs, zoom calls, Skype, iMessage and lot more.
One of the surest ways and guaranteed means of getting back your bitcoin is reaching out to hackerone975 @ gma1l c0m , they are certified and well experienced with all cryptocurrency trace and recovery. I was able to get back a large portion of my stolen bitcoin making use of their link. There are a lot of untrue recommendations and its hard to tell who is legit.
Incase you are in need of a real good and quality hacking services such as spouses cell phone hack, email hack, bank account hacks and others, hackerone975 is the best at that. I decided to hire him after a long history of disappointments from other fake hackers and he really surprised me by helping with every hacking help I needed, contact him and get yours done. Honestly you will thank me later so Contact there email hackerone975 @gmail com
Excellent and professional investigative services. I hired Mr JOSH for a very private and difficult matter of hacking my husband’s phone and he far exceeded my expectations. He helped me get some info such as whatsapp, facebook, text messages, call logs and even phone conversations that I needed for proof of his secretive affair. The first time we spoke, we had a very long phone consultation in which he gave me all my options that he could think of to resolve my case, and he even recommended I try other options before hiring him, which shows that he is honest. I decided to hire him and I am glad I did. He is a fantastic investigator and a great person; to all loyal partners out there if you have a dishonest partner don’t hesitate to send him a mail. He is also very good at fixing credit. Contact: hackerone975 @gmail com.
My Ex Boyfriend has always threatened me on leaking my nude and sex tape to my husband for the past 5 months now, he always collects money from me whenever he feels like. But all thanks to this hacker called russiancyberhackers @ gmail. com this hacker wiped all my nude pulse sex tapes out of my ex boyfriend phone and today am a free woman. I really appreciate you russiancyberhackers @ gmail. com
believe my boyfriend is cheating on me since I introduced him to a girlfriend of mine, he has changed completely. They both keep on denying. I need access to whatsapp and messenger to know the truth and finally find again peace of mind. All thanks to hack4wise @gmail com that hack my boyfriend phone within 4 hours , He allowed me to get all his messages and calls right from my phone anywhere and anytime,
A very big thank you to anonymousmaskhat@gmail. com for helping me hack into a WhatsApp business account without any form of trace. Am so happy
People find it hard to stay committed again. It’s becoming a difficult thing. Getting information & data you need is quite not a big deal. Sometimes the truth needs to be unveiled by whatsoever means necessary. The latter of the case should always be reckoned with, of which it would be known eventually what would be the data at hand afterwards. definitely contact Sam would do justice on this intercepting with wares and you will have me to thank later.I finally caught him red handed…
They also have refund policy if you wish not to further with your job.Contact him via
Email on;hackrontech @gmail com.
After getting in contact with jeajamhacker @ gmail. com I now know who my husband sneaks out at night to talk to over the phone after a successful phone hack with the help of jeajamhacker @ gmail. com. thank you so much jeajamhacker @ gmail. com
I felt so sad after I made some silly investment plans. I lost over 120,000 to this company called Tradixa. I couldn’t even tell anyone about what happened to me because I was so ashamed of myself until Jim a recovery expert from Recover Coin Rescue Team helped me recover all that was taken away from me and eventually exposed them to the authorities.(hackrontech @gmail com) and recover lost or stolen funds/coins.
I recently had the pleasure of hiring Kingston@cyber wizard.com, to track and recover money I lost to a fraudster, and I must say, the experience was outstanding. From the moment I contacted them, I was responded to promptly by the knowledgeable and friendly cyber expert. He took the time to listen to my concerns and provided expert advice on the possible solutions. What impressed me the most was the transparency and honesty exhibited throughout the process. The team at kingston@cyber wizard.com kept me informed every step of the way, explaining the steps in detail and providing reliable options. Not only did they complete the job promptly, but they also went above and beyond by performing a thorough evaluation and offering preventive measures recommended to ensure future occurrence. I highly recommend kingston@cyber wizard.com to anyone in need of reliable and trustworthy hacker/cyber wizard to track and recover lost money or assets. Their exceptional service, expertise, and dedication to customer satisfaction have earned my trust and review.
Hackron Group of Hacker save My Marriage I was a victim of Marriage cheats from my husband without knowing he has a family outside our Marriage and has been spending my money on them I never know he was capable of such but due thou the recently way he starts sneakily around I got suspicious of him and was in need of a Hacker to spy on him without no doubt my suspicious was true. Wizard Hackron Hacker got me proof of his message and calls and the address of other families where he goes frequently if you have such a cheating partner contact him via [hackrontech @gmail com].
I am extremely overjoyed. I followed my guts to trust Hackerone975 to assist me in claiming back my $852,000.00 invested asset. I am eternally indebted to them, their professionalism in tracing and recovering cryptocurrency is 5/5. And their support team, OMG, they restored my faith in cyber security. They offer free forensic analysis so there is absolutely nothing to lose rather you gain more knowledge for free. For their consultation: hackerone975 @ gma1l c0m
My step mom has been cheating on my dad for a while now but my dad never knew or suspected until I caught her red handed, but there again my dad will never believe me so I needed proof and with the help of spyexpert0@gmail. com I got the proof I needed after hacking into my step mother’s phone remotely and I presented the results to my dad. I just want to really appreciate spyexpert0@gmail. com I have never had the thought to hack anyone’s phone but I had to do this for my dad and you came through for me at a very affordable price thanks once again.
Cheating is a deal breaker for me , I always told the previous men I’ve had relationships with, the moment you are unfaithful is the moment you end our relationship. If I’ve ever felt so disconnected from my partner that I have felt myself drawn even into a hypothetical affair in my mind, I end the relationship. I’ve been in many abusive relationships (that I ultimately ended) but never once have I been unfaithful. Why? Because no failing relationship is worth sacrificing my morals and integrity for. No matter how it unfolds with a partner, there should be a base level of respect and empathy towards them as a human being. A failed relationship will not pollute your mind and foster insecurities anywhere near as being on the receiving end of adultery. I didn’t know what was happening all along for years that he’s been cheating until I met Hackerone975 at g ma il c om
Great service delivery. I am here to thank Ethical Hacks services and to also let people know that your services is the real deal and very reliable. I now have complete access to see and monitor all my husband’s chat messages on WeChat, i have been able to retrieve and recover all his deleted messages also, all thanks to you. This way i will get to know if he has been honest with me or not and if he is cheating on me. All this wouldn’t have been possible without your great help and assistance. text him on hackrontech @gmail com.
Thank you so much darkhatthacker @ gmail. com, with the proof and evidence you provided for me when I suspected my husband was cheating on me. Am happy to tell you openly that I won the divorce court case without stress now I can be a happy woman again. Thank you once again
Its a 100% possible to hack with the support of a professional ethics was hired by my best friend Henry; CYBERWEBPRO1 @ GMAIL . COM (HENRY GOBLETS) ) to hack his cheating wife device with just her number .
I was ignorant about a lot of things, I thought hacking was something very easy and i fell for a lot of scammers, including MSPY who lied and took my money but i met Cyberwebpro1 and he made me understand a lot of things.. he was amazing and really assist me get in my wife phone and track her location and also found out she has been planning to take everything and move to Mexico with her new lover .. this was really a shock to me and I feel bad after all I did for us… I really appreciate them
( CYBERWEBPRO1 @ GMAIL . COM ) Marriage is sweet, Love is also sweet but i don’t see why after getting married to my dream man he still cheated on me with his EX girlfriend though i had try breaking into his IPHONE since last year but still not getting access to his phone since then i just try to swallow all my husband had been doing but i can’t take it any more so i came in contact ( gmail of CYBERWEBPRO1 @ GMAIL . COM ), with his help I had access to my husband’s phone without touching his phone. I had full information of his chats with his ex-girlfriend last year. With all I saw, I don’t think I can move on with the marriage. He went as far as telling the girlfriend that I have been his wrong & i beat her up almost everyday. I was so disappointed & I called off the marriage..
Henry TechGuy ( CYBERWEBPRO1 @ GMAIL . COM )
It is heartbreaking and very disappointing to feel not loved and appreciated enough because if you are loved and appreciated enough by your partner there will be no need for him to cheat and give any attention to any woman other than yourself, I felt this way for so many years without knowing what to do and I couldn’t leave him because there was no concrete evidence to back up the feelings I had and none of my families believed me when I told them I think my husband was seeing someone else so I was determined to prove it, I went searching online on how to hack or spy my husband phone without him knowing then I saw a lot of people recommending Henry TechGuy as the best in the game well I wasted no time in contacting via on gmail and he gave me full access to his phone I was able to get the evidence needed to divorce him please don’t waste time being unhappy. CONTACT HIM VIA GMAIL CYBERWEBPRO1 @ GMAIL. COM/1(503)877 4273
Finding out that your partner has been unfaithful could be distressing. There may be a crisis in your marriage or other connection that ends up wrecking it. Although it is normal to want to know to find out the truth for yourself which you can by hiring a professional hacker ( Cyberwebpro1 @ Gmail Com / 𝖳𝖾𝗑𝗍: +1 (503) 877-4273 ) to help you gain access to his/her devices and have a look for yourself remotely without finding out any traces. I trust his service which is why i recommend it openly. There is rarely a clear- cut reason why someone would be unfaithful. It might have something to do with your partner’s background, it might be an indication of other problems in your marriage or relationship, or it might have nothing to do with you, your marriage or your relationship at all. Regardless of the cause, As you decide how to move on, you’ll have a lot of challenging feeling to work through and things to think about which the hacker will help you with guidance through the divorce process if necessary. You have to find outy the truth yourself rather than believe in rumors.
Contact Harry Goblets and his expertise services he delivers desired results
𝖤𝗆𝖺𝗂𝗅: CYBERWEBPRO1 @ GMAIL .COM
𝖳𝖾𝗑𝗍: +1 (503) 877-4273
I will suggest you contact a professional hacker if you need to hack your wife’s phone and social media account . He is a genuine and reliable hacker. I hired him from DARKWEB when I suspected my wife was cheating on me and hiding her phones. He got me access to bascially everything without her noticing she’s been hacked( exactly how i wanted it). I was able to see her old messages and new messages, call records, galleries and also deleted text messages. He completed the hack in few hours of contacting him. CYBERWEBPRO1 @ GMAIL .COM/+1 (503) 877-4273
My boyfriend took a break from our relationship just to cheat on me and I found out with the help of verifiedprohackers@gmail. com after I requested for a complete phone hack of my boyfriend’s phone, I saw how my boyfriend flirt so much with girls on his WhatsApp messages, iMessages, text messages and deleted messages. Thank you so much verifiedprohackers@gmail. com for your services, it really helped.
Hi everyone, I feel I should really let you all know about the person you should contact when you are in dire need of hacking and top notch spying services in person of CyberWEBPRO1 via his mail (CYBERWEB.PRO1@GMAIL.COM). It was this person who helped me out with my college grades when I needed an upgrade desperately when I could not do well due to working in between jobs as I had a family to fend for. He also does offer other services relating around hacking like expunging criminal and driving records, spying on cheating girlfriends/boyfriends/spouses. I have referred many of my friends to him, and he really helped them out and they are still very grateful till date. Please contact him on GMAIL. Your happiness is one mail away.
Hi everyone, I feel I should really let you all know about the person you should contact when you are in dire need of hacking and top-notch spying services in person of CyberWEBPRO1 via his mail (CYBERWEB.PRO1@GMAIL.COM). It was this person who helped me out with my college grades when I needed an upgrade desperately when I could not do well due to working in-between jobs as I had a family to fend for. He also does offer other services relating around hacking like expunging criminal and driving records, spying on cheating girlfriends/boyfriends/spouses. I have referred many of my friends to him, and he really helped them out and they are still very grateful till date. Please contact him on GMAIL. Your happiness is one mail away.
I got a WhatsApp hacked successfully with the help of russiancyberhackers@gmail. com with no trace.
If anonymousmaskhat @ gmail. com has ever worked for you please come out, give this hacker 5 stars reviews because this hacker is a genius and deserves to be appreciated, I just got my spouse iPhone 15 hacked with the help of anonymousmaskhat@gmail. com, God!! This still feels like a dream. Thank you so much anonymousmaskhat@gmail. com you are the best..
Have you ever wanted to spy on your spouse phone or wanted to monitor their phone. you may want to know what is happening in their life or how they are communicating with someone else. or maybe you want to protect them from ex either way. you can contact hackrontech @gmail com talks about it with kelvin. you want to hack your husband whatsapp account text messages on iphone or android phone remotely and provide ways of doing it without installing any software on the target device. you will get complete access to whatsapp, facebook, kik, viber, messenger, text messages and other app on the phone for better information.
A great hacker is really worthy of good recommendation , Hackerone975
really help to get all the evidence i needed against my husband and
and i was able to confront him with this details from this great hacker
to get an amazing service done with the help of Hackerone975 contact him on: Hackerone975 @ gmail com
It’s unfortunate that as a footballer that I am, my wife cheats on me whenever am out of the state for trainings with my team and It was so easy catching her red handed as I was able to hire jeajamhacker@gmail. com to have her phone tracked down and monitored that was how I was able to see how I was cheated on. Thank you so much jeajamhacker @ gmail. com
I was having real life problems when my friend recommended William to me. I contacted him because my business partner was shaking me, stealing money from the business and also my spouse was always up at odd hours clearly been cheating on me, so the hacker remotely hacked into their devices and granted me total access to their devices without their knowledge. I was overwhelmed that I could see their hidden finances that were off the record and read their texts, see new and deleted pictures, emails, call logs, Facebook, WhatsApp, Snapchat, emails and all that. Now it’s not just suspicion, I have facts and evidence against them… His email is hackrontech @gmail com.
Please beware there are many fake bitcoin mining/clouding out there, I have been a victim once but now a certified blockchain consultant and I know better. The whole plan was so smooth I could not doubt it. Bitcoin is actually a great investment option but one thing I discovered over time is that it is not possible to mine bitcoin so don’t be deceived. I invested $25000 on a particular website called eurekaminingblock, I monitored the profit yielding but was told to open a new blockchain account to receive my payout. A public wallet was imported into the account and I was made to believe that was my profit. The bitcoin was labelled non spendable and it took me 2 years to be able to access it without the knowledge of the company. The non spendable bitcoin is the scam out there now and a lot of people are falling victim of it. I found CM (a recovery expert and trader) on Quora who helped me access a significant part of my investment together with the profit without the knowledge of the company. You can reach him through his email :hackrontech @gmail com
My wife had a night stand with another man on her birthday while I was out of town and I got all this informations with the very help of spyexpert0@gmail. com
I was frustrated and depressed when i noticed my spouse was cheating on me and there was nothing i could do about it, one day i saw an ad by this hacker and decided to contact him we got to talking and he has been helping me ever since; right now i am in the final stages of my divorce getting what i deserve all thanks to them . you should contact him if you have any legit hacking related issues hack4wise @gmail com
How I got back stolen crypto currency coins and tokens from telegram scammers: People all across the world are hearing about the quick profits that early Bitcoin and other coin investors are making and want to get in on the action. But be aware that where there is big money, there are other companies who are abusing and exploiting the situation. Such was my experience when a phoney telegram group admin contacted me and sent me a phishing link containing my 12 recovery passwords. These nefarious individuals obtained access to my cryptocurrency wallet and stole all of my coins and tokens, totaling more than $230,000. Due to this situation, I was in a deep state of despair. I was perplexed until a telegram group member directed me to (hackrontech @gmail com) . This restorative agent is truly a gift from God. After I explained my situation, the circumstances of the incident, and the needs for my recovery programme, it took them less than a week to track down and retrieve all of my tokens and coins. They also assisted me in hacking the perpetrator’s wallet, and all of my monies were returned to me. I’m awestruck, overjoyed, and grateful. Without this specialist, I’m not sure what I’d do. They specialise in chargeback disputes, and their staff is trained to spot these types of con artists. If you’ve invested in cryptocurrency and think you’ve been duped, get in touch with their specialists right awayand they will help you recover your losses.How I got back stolen crypto currency coins and tokens from telegram scammers: People all across the world are hearing about the quick profits that early Bitcoin and other coin investors are making and want to get in on the action. But be aware that where there is big money, there are other companies who are abusing and exploiting the situation. Such was my experience when a phoney telegram group admin contacted me and sent me a phishing link containing my 12 recovery passwords. These nefarious individuals obtained access to my cryptocurrency wallet and stole all of my coins and tokens, totaling more than $230,000. Due to this situation, I was in a deep state of despair. I was perplexed until a telegram group member directed me to (hackrontech @gmail com) . This restorative agent is truly a gift from God. After I explained my situation, the circumstances of the incident, and the needs for my recovery programme, it took them less than a week to track down and retrieve all of my tokens and coins. They also assisted me in hacking the perpetrator’s wallet, and all of my monies were returned to me. I’m awestruck, overjoyed, and grateful. Without this specialist, I’m not sure what I’d do. They specialise in chargeback disputes, and their staff is trained to spot these types of con artists. If you’ve invested in cryptocurrency and think you’ve been duped, get in touch with their specialists right awayand they will help you recover your losses.
If your credit is not as clean as you want it to be I assure you that Green water credit is the perfect specialist for your job. It was a perfect credit solution to my credit profile, I had all negatives removed and my score had a boost of 250 points. It helped me acquire my new home for my family. I recommend (greenwatercredit at GMAIL dot COM) for any credit related issues. He is 1005 genuine and reliable.
I was initially doubting the work of A great man hackrontech @gmail com but I decided to gave them a try since what I wanted really
worth the risk but honestly this team was so amazing in less than1 hr I
was able to locate my wife’s location without asking her and all her
text messages with her call conversations keep coming to my phone , this
works like a magic so I will say u contact this team for professional
hacking service they are good at it
hackrontech @gmail com
Technology has seeped into every nook and cranny of our relationships, providing both parties to stay connected and a Pandora’s box of potential secrets waiting to be uncovered. Enter Cyber Genie Hack Pro, the key to unlocking those digital mysteries. The age old problem in almost all relationships is Trust. One minute you’re sharing your deepest thoughts over a candlelit dinner, next, you’re left wondering if your partner’s emoji use is hiding a deeper, darker truth. Why should you care about decoding your wife’s secret messages? Aside from the obvious curiosity that comes with uncovering hidden truths, understanding what’s going on behind the screen can help bridge the gap between what’s said and what’s unsaid in your relationship. Plus, who doesn’t love a good digital detective story? Now, onto the main event – how does this enigmatic Cyber Genie Hack Pro work its magic? Prepare to be dazzled by the software’s features and the technical wizardry behind retrieving those elusive deleted messages. With a wave of its virtual wand, Cyber Genie Pro promises to unearth deleted messages, uncover hidden conversations, and provide you with a front row seat to the digital drama playing out in your wife’s messages. This software claims to reveal it all. Talk about a digital fairy godmother! So, you’ve successfully set up Cyber Genie Pro on your chosen devices – now what? It’s time to sit back, relax, and watch as the software works its magic, recovering and presenting you with those secret messages you’ve been yearning to see. From decoding cryptic conversations to analyzing the tone and context of each message, get ready to immerse yourself in a digital world of intrigue and discovery.
Email :_Cybergenie (@) Cyberservices (.) Com
_Telegram (@)CYBERGENIEHACKPRO
Have always thought my husband is cheating on me via WhatsApp which I have always been on his WhatsApp just to catch him red handed yet I didn’t see any trace of him cheating until I came in contact with hackrontech @gmail com after the phone hack this hacker did for me I found out that my husband has numerous girlfriends on his snap chat and communicates with them often I was also able to check his deleted text messages and what I saw there was heart breaking. hackrontech @gmail com, am grateful for this powerful results thank you.
Been stalking my husband remotely for over 6 months now without him even noticing what is going on and not knowing I know about all his dirty talks with other young girls out there , buying them gist items and keeping them in a hotel rooms while he sometimes comes back home Late then Lies when you ask of his whereabouts , I made contact with one of his side chicks who was 24 and gave her a serious warning and embarrassment of her Life . I was able to get the informations I needed with the help of hack4techspy @gmail com , The best when it comes to this , he saved my marriage and I’m grateful.
Do you need hackers for hire? Do you need to keep an eye on your spouse by gaining access to their emails? As a parent do you want to know what your kids do on a daily basis on social networks ( This includes facebook, twitter , instagram, whatsapp, WeChat and others to make sure they’re not getting into trouble? Whatever it is, Ranging from Bank Jobs, Flipping cash, Criminal records, DMV, Taxes, Name it, We can get the job done. They are a group of professional hackers with 10 Years+ experience. Contact at ( hack4wise @gmail com ) … Send an email and Its done. Its that easy, try us out today.
verifiedprohackers@gmail. com is a very reliable hacker, and has never disappointed the few times I used his services. Thank you verifiedprohackers@gmail. com for being real to me and to others.
For a few months now I suspected that my husband was cheating around with other people, however I had no solid proof or evidence. I stumbled across this website which I found a great recommendation to hack4wise @gmail com that helped me see who my spouse was text messaging/calling. I also tracked my husband’s location, I got this proof to my lawyer and this was the strong document he used in my divorce, all thanks to hack4wise @gmail com he helped me a lot, anyone who needed a hacking service. he will help you.
I caught my wife and her pastor having an affair with the help of russiancyberhackers@gmail. com, After the phone hack i saw so many things, the likes of there chats and also got all the video calls they did in the past in fact this hacker is a guru. As i speak I have so many evidence and I will expose them in no time.. thank you so much russiancyberhackers@gmail. com
I am so happy to introduce you to (Recovery Nerds) who swift into quick action when I reported my scammed money from Bitcoins investment to them as soon I followed their procedures, I was scammed for the sum of ($429,530), from Bitcoins investment and (Recovery Nerds) They help me recover my money back in 24 hours, I recommend you all to (Recovery Nerds) at their support Mail: mailus @ recoverynerds. com, WhatsApp number: +15143122803, Website: recoverynerds.com/ They deliver as promised.
I thought I should share this so as the reach others with bad credits and in need of assistance like I was. I was trying to finance a new home for my family a few months ago and I was unable to due to poor credit till I saw a post here about gearheadcypanacea dot com. I contacted them and so far I have been very pleased with the result as my score has gone from 490 to 780 in 3weeks. Reach them on (6,0,5 6,0,3 9,7,8,3 gearheadcyberpanacea AT g mail. com) if you have poor credits and you will be amazed by the outcome.
Thank you so much anonymousmaskhat@gmail. com for delivering on an iPhone 15 phone hack 100% without any notifications or trace by the victim.
Having access to my spouse phone is what i have always wanted but the issue
i had was that a lot of scammers are on the internet disguising. I needed
to be very careful so i don’t fall victim. I saw a lot of review about
TECHWIZARD64 AT GMAIL DOT COM and i decided to give them a try! I requested for
past deleted messages and they said they would be able to provide me with that
also GPS live location and this made me amazed, not only this they explained everything
how I would be able to view everything on my spouse phone through my phone without any traces..
They got the job done in just 24hrs. This is what they are specialized in just incase you want to gain access
into your spouse phone you can contact them with the email above. Thank me!
THIS GENIUS VADIM ALBERTO WITH THE EMAIL VADIMWEBHACK@ GMAIL. COM HELPED ME READ ALL MESSAGES FROM AN IPHONE WITHOUT PHYSICAL ACCESS.
To be honest, if your partner is acting off or you have trust issues I think it’s best to know where you stand in their lives before committing to something as sensitive as marriage. I almost ended up in a marriage that would have wrecked me. The person I was planning to spend the rest of my years with was already married to someone else in a different country. Apparently I was just supposed to be a money bag. How did I find out? Vadim Albert literally saved me. My gut feeling kept telling something wasn’t right. The sneaking out to make calls, the obvious lies and many other red flags. I had to search for help and a friend of mine whom Alberto had helped erase some bad records gave me his contact. If you need help, I would advise you reach Alberto via Email: Vadimwebhack@ gmail. Com OR WhatsApp: +.1.8.1.4.3.2.9.3.6.7.5
He offers many other services like credit repair, can make you eligible for loans, boost school grades and a lot others I can’t mention here.
So much to write about hackerone975 at gm ail c om which if I start I will cover the whole internet with the good jobs
this hacker has done for me so far but right now all I can say to Hackerone975 is, I will forever be grateful to you,
you really saved me from sudden heart break from my spouse with your hacking services I found out right on time
before my spouse could execute his plan with his side chick.
There are lots of fake hackers online and i don’t wish anyone out there should fall victim in there hands, i can only recommend ( Hackerone975 )and he has been doing a great job. can’t write all the good works he has done for me and my friends but his work is Accurate, Quick responds, Quality service and many more. He offer services like access to Facebook chats, WhatsApp messages, Phone texts, call logs, browser history, recover deleted files, chat history, gallery folder, GPS locations, upgrade result, delete criminal record and many more…if in need of any of such service, contact (hackerone975 @ gmail com).
Hacking a mobile phone is usually something that requires hiring an expert to get it done for you to get your desired result. These mobile hacks actually work fine but most people have problems using it because bulk of the job is done and highly dependent on the hacker. In most cases, the only way you can get it done yourself is if you really know how to hack. Otherwise, your best bet will be to hire a professional hacker, and I recommend ; hackerone975 at gmail com , I have used he service and his is highly professional, he’s the best and he will give you exactly what you want. CONTACT ; hackerone975 at gmail com
CONTACT US FOR ALL KINDS OF HACKING JOB @ PROFESIONALHACKER112 AT GMAIL DOT COM We offer professional hacking services , we offer the following services;
illegal card hacking
Removal of the old credit score
University of change of notes
Bank accounts hack
Procedures of crime
Facebook hack
Twitters hack
personal mail accounts
Grade Changes hack
Policy blocked on site
server crashed hack
Skype hack
Snap chat hack
Dates hack
Word Press Blogs hack
Individual Computers
Control devices remotely
Burner Numbers hack
Verified PayPal accounts pirate
Any social network account you make
Auto and iPhone Hack
Text message intercept text
Trapping in the mail
credit card for free online transactions
Credit Card and Credit Card Blank ATM
Untraceable IP etc.
Contact : PROFESIONALHACKER112 AT GMAIL DOT COM
NOTE they are the solution to all your hacking problem
I’ve been a victim of infidelity and I can tell you vividly that it hurts, and worse if you couldn’t get an evidence to proof your sanity. Even though I have discourage my friends severally about hiring a private investigator to catch their cheating partners, I resorted to hiring one before my divorce. My partner hid her affair too well and I had no evidence to prove her infidelity to the court so I had to go back to my friend who I’m grateful for referring me to the review about a private investigator who he worked with on (hackrontech @gmail com), I told them the service I’m needing from them and why I need it. Their services were topnotch which made working with them very easy, they got me everything I needed within few hours and it was amazing. I never knew technology has been so advanced that I can see everything wanted at the tip of my fingers (forgive me I’m not a techie and neither am I good at it), with their exceptional service, I was able to convince my lawyer on why I should get a divorce and start a new life.!
GOD!! I never knew hackers like darkhatthacker@gmail. com are this real. God bless you darkhatthacker@gmail. com for giving me the best services in catching and spying on my cheating wife..
I lost my job back sometime last year and my credit scores ran down in the low to 455. I enter the internet in search of help and I met with Aaron Swartz Credit Repair. My old friend introduced me to a Credit Guru AaronSwartzCyberServices A T gmail DOT com, Cell
I was taken advantage of by a fake crypto investment website. After putting in a fortune I found it hard to withdraw my ROI after couple of weeks of my investment and they kept requesting for more that was when I figured out i’ve been tricked for my funds. I search through the web for a genuine recovery expert then I found Donald Jackson recovery services I reached out to them via gmail at hackrontech @gmail com and they helped me recover my stolen funds within a twinkle of an eye. They are the best recovery expert with no hidden charges, upfront payment or percentage of the recovered funds. Write them now!
Catch your cheating partner redhanded in their sneaky ways when you hire hackerone975 @ gmail c0m. This was the expert that saved me from my cheating wife couple of weeks ago when I had a suspicion on her but couldn’t figure out exactly her ways. I was fortunate to hire this genuine tech pro to remotely access my wife’s cellphone and gave me access to her phone files ranging from iMessage, text messages, call history, Snapchat, gallery, videos etc. All these contents were both hidden, current and deleted files. This was how I got to know about her love affair with a colleague at her work place. I was shocked about all the details I retrieved but I’m glad that I’m freed from the shackles of a cheater. I’m currently in our divorce proceedings and this files are really helping me out in the court cases. Many thanks to hackerone975 @ gmail c0m for rendering this intellectual phone monitoring service. Em ail: hackerone975 @ gmail c0m ;. Extraordinary services
Why be in a relationship without rest of mind. always feeling like your been cheated on. i have been married for 7 years now but for couple of months i notice some unusual change in my husband activities like late night calls, hiding messages, delete photos and many more but when i try to talk to him about it, he complains i nag a lot so i decided to hire a genuine hacker which i got introduced to hackerone975 . After couple of hours with this expert , i was able to gain access to my partner phone without any physical touch . I got to see his hidden messages, social media, gallery , call recordings and more. anyone in need of a genuine hacker can reach out to [ hackerone975 @ gmail com ]
Guys be wise, do not make the same mistake I had made in the past, i was a victim of bitcoin scam, i saw a glamorous review showering praises and marketing an investment firm called AUBREY Investment Co, I reached out to them on what their contracts are, and i invested $30,000, which i was promised to get my first 15% profit in weeks, when it’s time of collection of profits, I got to know the company was bogus, they kept asking me to invest more and i ran out of patience then requested t have my money back, they’ve refused to answer nor refund my funds, not until Fred my friend introduced me to the Cryptocurrency Recovery Agency, after tabling my complaints, they were swift to action and within 36 hours, i got back my funds with the due profit, I couldn’t contain the joy in me. I urge you guys to reach the Crypto Recovery agency on their support email:(hackrontech @gmail com)
I’m not a review type normally I just use my product and leave . But here I am and that’s cause I’m super excited about this App , Mspy is fantastic but how much more can you explore this app , first annoying as I couldn’t navigate to the points I want , late gps update and still got my money deducted got me mad but I saw a review on a website months back about a professional hackers spyhackelite i wrote to him via spyhackelite @gmail com that he is the best to help you out on issues like this , I decided to give it a try , life itself is all about risk anyways but I’d definitely say it’s damn worth it
My mom and I bear the same name and her credit information gets put on my credit report a lot. It became a struggle for me and I felt like I was living in someone else’s shadow. When things weren’t paid or went into collection or judgment my credit took a hit so I needed them to make the correction, restore my credit and make it stop. No one could help until vladmir of thehackerspro Steeped in and corrected the mistake, restored my credit to high 750s and put a permanent stop to the constant report of my mom’s credit info on my credit report.now we are able to get a loan on our mortgage to purchase a property here in silicon valley.contact them on
hack4techspyh @gmail com
I appreciate kolarov monte for making me realise the truth to a certified hacker who knows a lot about what his doing. I strongly recommend you hire him because his the best out there and always delivers. I have referred over 10 people to him and all had positive results. He can help you hack into any devices, social networks including – Facebook, Hangout, iMessages, Twitter accounts, Snap chat , Instagram, Whatsapp, wechat, text messages ,smartphones cloning ,tracking emails and also any other social media messenger or sites. It’s advisable to hire a professional hacker. Thank me later. Contact him here.hack4techspyh @gmail com although he’s quite expensive so you have to be ready for the service,
MY CRYPTO RECOVERY EXPERIENCE 2024
WARNING: Scammers will stop at nothing to steal your hard-earned money! But, I’m living proof that JETWEBHACKERS can help you RECLAIM YOUR LOST FUNDS! I thought I’d lost my life savings of $58,000 after investing with a fake broker, promising me a whopping $187,000 profit to fund my urgent surgery. But, JETWEBHACKERS didn’t give up on me. They worked tirelessly to track down my money and recover it. And, after months of intense effort, they successfully recovered my entire investment – $58,000! I’m now able to focus on my health and recovery, knowing that I’ve been given a second chance thanks to JETWEBHACKERS. Don’t let scammers ruin your life like they almost did mine! If you’re in a similar situation, don’t hesitate to reach out to JETWEBHACKERS. They’ll be your champion in the fight against online fraud!”
CONTACT THEM VIA
EMAIL:jetwebhackers @ gmail .com
TELEGRAM: @jetwebhackers
THANKS TO RECLAIM FUNDS FIRM, I HAVE FINALLY RECEIVED MY LOST BITCOIN.
Seeking assistance recovering stolen cryptocurrency wallets, recovering cryptocurrency taken by scammers, or reporting a Bitcoin scammer to recover cryptocurrency? The safest course of action is to work with a reputable RECLAIM FUNDS FIRM Expert—a specialist with cyber areas of expertise that can retrieve cash that have been embezzled by fraudsters. After losing $273,000 to a fraudulent online investment organisation, I made numerous attempts to get my money back. I tried a variety of recovery firms, most of which ended up taking additional money from me. My former colleague informed me about RECLAIM FUNDS FIRM. I contacted the Expert and, upon presenting my reports, the Expert was successful in retrieving my money.
Get in touch with Wizard Williams Recovery through;e m a i l : reclaimfundsfirm (@) aol (DOT ) com
or Whats APP: (+) (65) – (9055) – (2242)
111 N BRAND BLVD.
18TH FLOOR GLENDALE CA 91203
After so many failed contact with some hackers, I finally got in contact with a credible hacker remotespywise @ gm ail c o m who gave me swift access to my spouse device. He also retrieve lost email, stolen funds and also retrieve lost wallets. You can also contact him for all other hacking services.
I came to find out that there was a lot of things going on in my marriage even with the way my husband act really loyal to me, he was really a cheat and comes back home clean and act like nothing happen, i was browsing through a blog online and got to read about WAYNE and decided to try him out and in less than 4 hours i got all i wanted, he helped me spy into his whats-app, Facebook, Instagram,twitter,Skype,call logs, IM, Emails, messages, retrieve all deleted messages also i will advice all married women to do a little check on there husband to know whats is really going on some act clean and are not clean at all, contact hackrontech @gmail com.
My husband has been frequently deleting all messages for the last couple of days from his phone and he didn’t know i was peeping at him, then i asked him why he was deleting all messages from his phone but he claimed that his phone memory was full and needed more space. Immediately I went in search of a hacker who can get me deleted information and contents from my husband’s phone and luckily for me i came across this reputable ethical hacker Me Fred, this hacker got the job done for me and provided me with results and i saw that my husband has been lying to me. He was simply deleting all pictures, call logs, chats and text messages between him and his secret lover so i wont get to see what he has been doing at my back. Thank God for reputable hackers who are ready to help. I must say am really impressed with the services i got from The hacker Detective and am here to say a very big thank you: contact him on remotehacker8 at gma il dot com
I’d recommend that y’all reach out to remotehacker8 @gmail com for a quality spy tech service. Their services are great and top notched.
Hire a Professional hacker to change your grade(s) no matter the numbers, distance is not a barrier. Don’t give your jobs to amateur or hackers wannabe HOW TO HIRE write to them on: (remotehacker8 at gmail com) & Wait for their fast response and tell you what’s next. it is as easy as that, they handle the rest.Stay safe
Are you interested in the service of a hacker to get into a phone, facebook account, snapchat, Instagram, yahoo, Whatsapp, get verified on any social network account, increase your followers by any amount, bank wire and bank transfer. Contact him on= hack4wise @gmail com
I am not the first to recommend him because his recommendations can be seen everywhere but I am doing this because I am very happy, I am very happy because I made the right choice and that right choice is me chosen to follow my instincts and go with the good reviews i saw about Remedy hacker, believe, if it’s not for that choice i made i would have still been in a very toxic relationship with my ex partner who was a serial cheat but all that is gone now thanks to Remedy hacker everyone deserves happiness that includes you so to get that happiness you deserve I reckon. contact the best in the game for spying and gaining access into phone remotely without having the device on your hands contact email ; hack4wise @gmail com
People cheats due to lack of being contented with their partner or some other reasons. You can’t trust your partner 100% cause you get to know different behavior in a person each day. if you suspect your partner is cheating it’s better to know the truth at once so you can get the peace of mind before it’s too late and you live a life full of regrets. You can’t do this on your own that’s why you need the assistance of an IT expert/PI to monitor and track all the activities of your partner in one swipe. Here is a good news, he can simply help you get this info without stress. Are you scared of being ripped off?? You don’t need to worry any longer he provides a reliable service and offers a refund policy which is strictly observed. You can write him at remotespywise @gmail com. for a wonderful and genuine services.
I hacked my spouse phone with the help of darkhatthacker@gmail. com Just to discover that my spouse has never blocked her ex but still in communication with him, I feel so broken and depressed but am glad I could find out on time with the help of darkhatthacker@gmail. com.
There are lots of fake hackers online and i don’t wish anyone out there should fall victim in there hands, i can only recommend ( Hackerone975 )and he has been doing a great job. can’t write all the good works he has done for me and my friends but his work is Accurate, Quick responds, Quality service and many more. He offer services like access to Facebook chats, WhatsApp messages, Phone texts, call logs, browser history, recover deleted files, chat history, gallery folder, GPS locations, upgrade result, delete criminal record and many more…if in need of any of such service, contact (hackerone975 @ gmail com).
I always stood against people trying to hack their partner’s phone, until my cheating husband gave me every reason to spy on him. I’ve been suspecting his attitude lately and I really loved my man, so I was eager to find out the reason behind his sudden change of attitude. I contacted Fred Hacker who was recommended by a friend and after a few hours of contacting him, he gave me remote access to my husband’s phone and I saw all his day to day activities and I was able to confirm he was cheating. You can reach him on g ma il through; hackerone975 @ gmail com
Life can be so cruel sometimes but even worst when you have a cheating partner. I got to discover my spouse was having an affair through the help of { REMOTESPYWISE @ GM AIL C O M } who gave me access to his device remotely without his notice. I got access to all social media apps, call logs and sms and deleted data and messages too. Do not be a victim to lies and mischief. Get in contact with him and stay safe
My husband has been frequently deleting all messages for the last couple of days from his phone and he didn’t know i was peeping at him, then i asked him why he was deleting all messages from his phone but he claimed that his phone memory was full and needed more space. Immediately i went in search of a hacker who can get me deleted information and contents from my husband’s phone and luckily for me i came across this reputable ethical hacker Me Fred, this hacker got the job done for me and provided me with results and i saw that my husband has been lying to me. He was simply deleting all pictures, call logs, chats and text messages between him and his secret lover so i wont get to see what he has been doing at my back. Thank God for reputable hackers who are ready to help. I must say am really impressed with the services i got from The hacker Detective and am here to say a very big thank you: contact him on hack4wise @gmail com
Are you dealing with internet hassle?, be it recovery of lost funds due to investments in cryptocurrency, stocks, shares in phony companies, tracking and monitoring of cheating spouse/partner, romance scams etc.It has never been made this easy.
I recently made use of Mr. Kingston service in monitoring and tracking my cheating husband who always uses his job as an excuse to cheat on me with numerous sidekicks, with the help and cyber prudence of Mr Kingston I was able to get all the necessary evidence and information, I also caught him in the act. Do well to contact him if you ever need such services.
CONTACT;KINGSTON@CYBER WIZARD.COM
I had a hunch about my wife cheating on me so I contacted a friend that referred me to cyberspacehacker. He helped me confirm my suspicions by granting me access to my wife’s phone where I was able to see for myself her messages and call log. Thanks to cyberspacehacker for saving me from a sad marriage. You can contact him on cyberspacehacker @ gmail dot com. If you are in the same position I was.
Have you ever wanted to spy on your spouse phone or wanted to monitor their phone. you may want to know what is happening in their life or how they are communicating with someone else. or maybe you want to protect them from ex either way. you can contact hackrontech @gmail com talks about it with kelvin. you want to hack your husband whatsapp account text messages on iphone or android phone remotely and provide ways of doing it without installing any software on the target device. you will get complete access to whatsapp, facebook, kik, viber, messenger, text messages and other app on the phone for better information.
RECOVER YOUR LOST/STOLEN BITCOIN WITH THE HELP OF CRYPTO RECOVERY WIZARD
When it comes to retrieving stolen bitcoin, CRYPTO RECOVERY WIZARD is unique due to its skill, dedication, and experience. Knowing the ins and outs of the cryptocurrency world, they work closely with law enforcement and utilize cutting edge methods to locate and track down stolen bitcoin. Their exceptional reputation in the bitcoin recovery services industry stems from their individualized approach and unwavering dedication to client satisfaction. My bitcoin was stolen, and although I reached out to several hackers who said they could help me get it back, all they did was take additional money from me in the process. Upon reaching out to CRYPTO RECOVERY WIZARD for support, all hope was reestablished. I was first skeptical, but CRYPTO RECOVERY WIZARD eventually managed to retrieve my bitcoin. Thank you very much. contact CRYPTO RECOVERY WIZARD for help to get your ust/stolen funds back and be happy.
Email: hackrontech@ gmail.com
EXPERT IN LOST CRYPTO RECOVERY;CRYPTO RECOVERY WIZARD. Do you need help in; Reclaiming lost Crypto Wallets, retrieving Crypto lost to Scammers, reporting a Bitcoin scammer to reclaim crypto? There is only one way to go about it, You should hire a legitimate Expert in Crypto Recovery Wizard, A specialized Expert with cyber specialties to recover scammed funds from swindlers. After losing $374,000 to an Online bogus investment company, I had tried countless times looking for a way to recover my funds. Most of the recovery companies I tried out ended up dumping me more funds. I came to learn about CRYPTO RECOVERY WIZARD through my old time Colleague, I got in touch with the Expert, and after submitting my reports, The Expert was able to recover my funds. Contact CRYPTO RECOVERY WIZARD via Contact Info; Email: hackrontech@ gmail.com
Marriage is quite a difficult task to handle, I’ve used a backend channel to monitor my partner’s activities in social media. It’s been a great experience using the tech skills of King (hack4wise @gmail com) to get into cellphone undetected, I’m vouching for him to handle such tasks for you too.
My husband has been frequently deleting all messages for the last couple of days from his phone and he didn’t know i was peeping at him, then i asked him why he was deleting all messages from his phone but he claimed that his phone memory was full and needed more space. Immediately i went in search of a hacker who can get me deleted information and contents from my husband’s phone and luckily for me i came across this reputable ethical hacker , this hacker got the job done for me and provided me with results and i saw that my husband has been lying to me. He was simply deleting all pictures, call logs, chats and text messages between him and his secret lover so i wont get to see what he has been doing at my back. Thank God for reputable hackers who are ready to help. I must say am really impressed with the services i got from The hacker Detective and am here to say a very big thank you: contact him on (( hack4wise @gmail com)
It was remotely done and professionally handled with few requirements. Things were not going well for me in my relationship, I was so confused and I didn’t know what to do. things became worse when my husband started telling me he needs to stay long hours at work almost every night for clubs and out with friends not knowing he was seeing someone else, it is good as dead when you cant take charge of your relationship because it was so surprising to me what was happening because he wasn’t lacking anything. But I was helped by Fred Hacker who monitored his activity and found out that he had been blackmailed by his past life and in the process he was sleeping with who was blackmailing him. It was terrible for me and if you want to catch your cheating partner, reach out to him and he’ll surely help you. Contact him on wisetechacker @gmail com
I always stood against people trying to hack their partner’s phone, until my cheating husband gave me every reason to spy on him. I’ve been suspecting his attitude lately and I really loved my man, so I was eager to find out the reason behind his sudden change of attitude. I contacted Fred Hacker who was recommended by a friend and after a few hours of contacting him, he gave me remote access to my husband’s phone and I saw all his day to day activities and I was able to confirm he was cheating. You can reach him on gm ail through; (( hack4wise @gmail com