August has been a busy month for software giant Microsoft as it released a series of security patches to fix vulnerabilities, many of which were tagged as ‘critical.’
The security patches were part of the Microsoft August Patch Tuesday update and contained patches for 48 vulnerabilities. 25 of these vulnerabilities were remote code executions which have a severity rating of ‘critical’ or ‘important.’
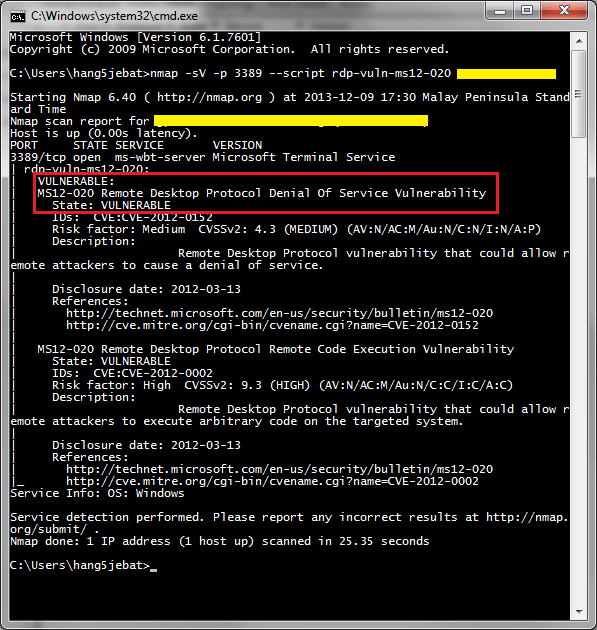
The worst among all the RCE vulnerabilities that has been fixed was the Windows Search related CVE-2017-8620. In a post published on Microsoft’s Security TechCenter, the company explained how CVE-2017-8620 could be exploited. It read:
“A remote code execution vulnerability exists when Windows Search handles objects in memory. An attacker who successfully exploited this vulnerability could take control of the affected system. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights.
To exploit the vulnerability, the attacker could send specially crafted messages to the Windows Search service. An attacker with access to a target computer could exploit this vulnerability to elevate privileges and take control of the computer.
Additionally, in an enterprise scenario, a remote unauthenticated attacker could remotely trigger the vulnerability through an SMB connection and then take control of a target computer.”
#Microsoft fixed 48 Windows vulnerabilities, 25 tagged as critical.Click To TweetThe company then said that the vulnerability had been addressed by correcting how Windows Search handles objects in memory.
The Patches and Vulnerabilities
The CVE-2017-8620 bug was said to affect several versions of Windows 10, Windows Server 2012, and Windows Server 2016. Jimmy Graham, Director of Product Management at Qualys said:
“While an exploit against this vulnerability can leverage SMB as an attack vector, this is not a vulnerability in SMB itself, and is not related to the recent SMB vulnerabilities leveraged by EternalBlue, WannaCry, and Petya.”
The security update also included a patch for another RCE connected to the Windows Hyper-V or the CVE-2017-8664. As explained in Microsoft’s Security TechCenter:
“A remote code execution vulnerability exists when Windows Hyper-V on a host server fails to properly validate input from an authenticated user on a guest operating system. To exploit the vulnerability, an attacker could run a specially crafted application on a guest operating system that could cause the Hyper-V host operating system to execute arbitrary code.
An attacker who successfully exploited the vulnerability could execute arbitrary code on the host operating system. The security update addresses the vulnerability by correcting how Hyper-V validates guest operating system user input.”
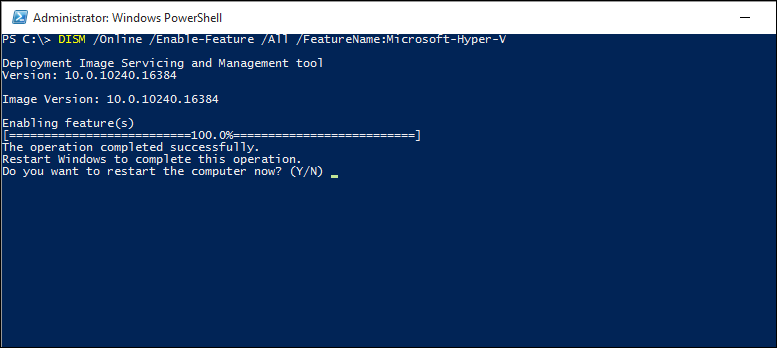
Apparently, an attacker just needs to run a malicious application on a guest OS that could force the Hyper-V host operating system to execute the arbitrary code. While Microsoft confirmed that the bug had been fixed, Zero Day Initiative said bugs like these need extra attention.
“Although neither is publicly known nor actively exploited, this bug certainly warrants extra attention. Back at the 2017 Pwn2Own competition, a Hyper-V escape like this one would have earned the contestant $100,000,” ZDI commented.
Another critical remote code execution flaw that was fixed was in the legacy JET database engine which could allow an attacker to take full control of a computer when exploited.
By exploiting the RCE bug, an attacker could trick any user to open a malicious database file from an email as part of a spearphishing campaign. However, the software giant claimed that the bug was ‘unlikely’ to be exploited.
A patch for the CVE-2017-8633 vulnerability was also part of the update. In a statement to SC Media, Chris Goettl, Product Manager at Ivanti, said:
“CVE-2017-8633 is a vulnerability in Windows Error Reporting which could allow an Elevation of Privilege exploit. The attacker could run a specially crated application to cause an error that could allow them to elevate their privileges enough to gain access to sensitive information and system functionality.”
The Tuesday update also included for the first time a unique Linux patch. Bobby McKeown of Rapid7 said:
“This is the first time we have seen vulnerabilities patched on the Linux subsystem under Windows and CVE-2017-8627 (Dos), and CVE-2017-8622 (Privilege Escalation) are the first of their kind.”
McKeown also praised Microsoft for patching some publicly disclosed vulnerabilities.
In addition to the vulnerabilities that were mentioned, Windows 10 has an additional vulnerability, the CVE-2017-8627, which was said to be a flaw in Windows Subsystem for Linux. The RCE could enable a Denial of Service attack and could be exploited by attackers by running a specially crafted file.



















I have finally recovered all the lost crypto which i made to some fake crypto trading company with the help of Jeff Silbert a financial recovery expert. After months of waiting for this company to accept my withdrawal request which they denied, They locked my account and stopped responding to my mails. he helped me to recover all my money from them. She trusted and honest All thanks to Jeff and you can contact him via em ail on jeffsilbert 39 g mail Com or whatapp + 1 (470 ) 469-9769